Governance Pipeline
End-to-end governance with security levels, de-identification, and audit trails
Overview
The OpenRails governance pipeline provides a comprehensive framework for data protection, access control, and compliance. It integrates data labeling, de-identification, security levels, and audit logging into a unified system that operates across the entire data lifecycle.
Security Levels
OpenRails supports multiple configurable security tiers. Assign tiers to content based on sensitivity, and users only see content at or below their clearance level. Tiers range from public (non-sensitive, available to all authenticated users) through increasingly restricted levels up to the most sensitive classification, which requires explicit individual grants and admin approval. Organizations can customize tier labels and access rules to match their existing data classification policies.
Governance Pipeline Stages
Content Classification
When content enters OpenRails (via upload, crawl, or connector sync), it is automatically classified using data labeling rules. Labels determine the security level and applicable de-identification rules.
De-identification
Content flagged as containing PII is processed through de-identification rules. Pattern, dictionary, and category rules detect and mask sensitive information before it enters the vector store.
Access Control Enforcement
Security levels control who can access content at every stage:
- Data Lake Access — Users must have the required clearance level
- RAG Retrieval — Only chunks matching the user's clearance are returned
- Agent Execution — Agents inherit the executing user's clearance level
Output Filtering
LLM responses are filtered before reaching the user. Any PII that was not caught during ingestion is masked at output time as a second line of defense.
Audit Logging
Every access, modification, and governance decision is recorded in the audit trail. Logs capture who accessed what data, when, and what governance rules were applied.
Audit Trails
The governance audit trail provides a complete record of data interactions:
| Event Type | Recorded Data |
|---|---|
| Document Access | User, document, timestamp, access type (view/download/RAG retrieval) |
| De-identification Applied | Document, rules triggered, PII types detected, masking applied |
| Classification Change | Document, old/new classification, user who changed it |
| Access Denied | User, resource, required clearance, user clearance |
| Export/Sync | Data exported, destination, governance rules applied |
Setting Up the Pipeline
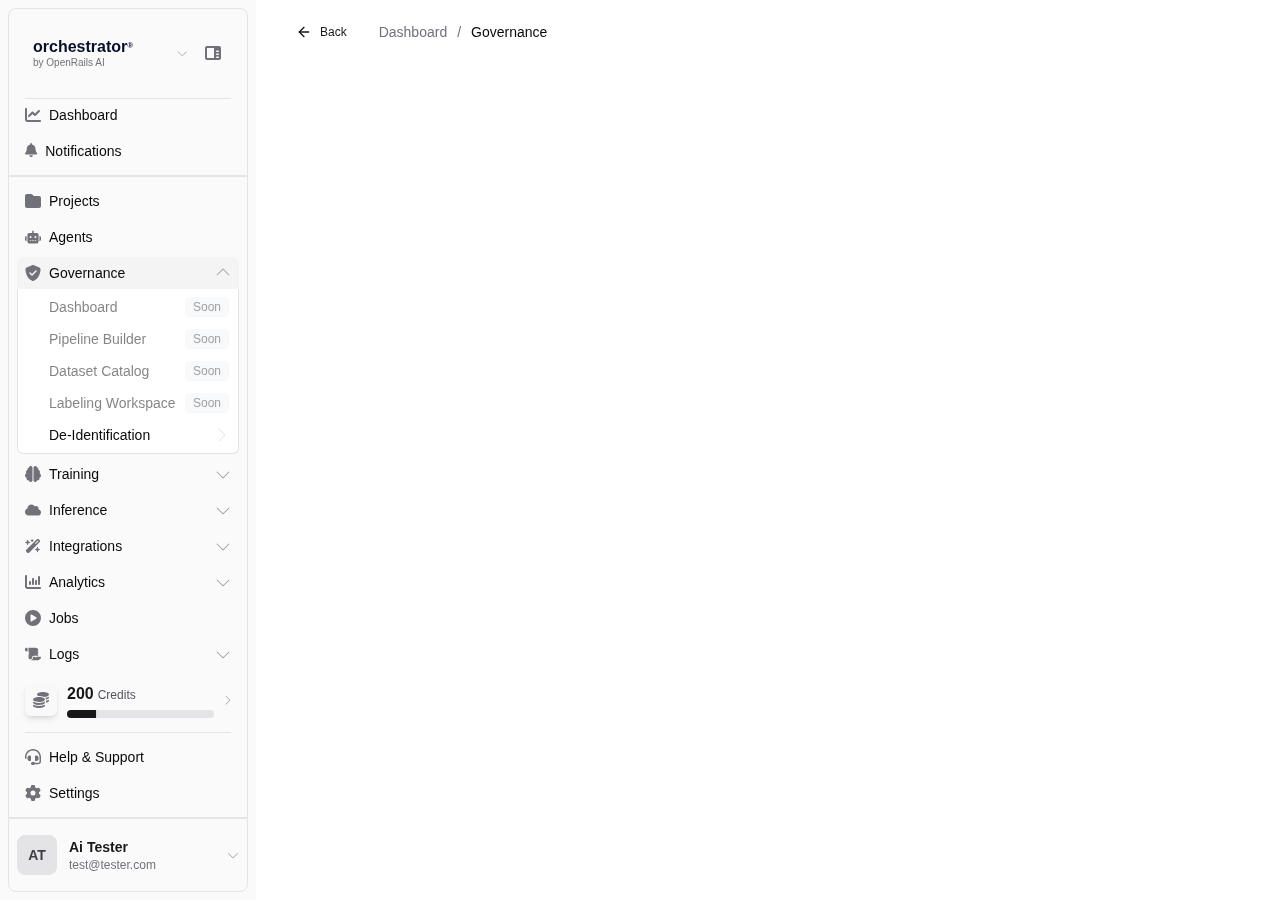
Define Security Levels
In Governance > Settings, review and customize the security level definitions for your organization.
Create Classification Rules
Set up auto-labeling rules in Data Labeling to automatically classify incoming content.
Configure De-identification
Create de-identification rules in De-identification for each type of PII your organization handles.
Assign User Clearances
In user management, assign security clearance levels to each user. Users can only access content at or below their clearance level.
Enable Audit Logging
Ensure audit logging is enabled in Governance > Settings > Audit. Configure log retention period and export destinations.